Technical Alert
ISA is recommending US companies and Canadian companies that have operations in the US to reassess their cybersecurity controls following warnings from the bulletin distributed by the Department of Homeland Security (DHS). Homeland security issues and threats information was provided by the National Terrorism Advisory System (NTAS). CISA Alert AA20-006A
These threat actors are known to use the following tools, including and limited to, Mimikatz, EternalBlue, NBTScan, Empire, DroidJack, Nanocore, njRAT, Netwire, QuasarRAT, Remcos, SHAMOON. These threat actors are also known to use the techniques such as spearphishing with malicious URLs, .hta or .vbe attachments, bruteforcing credentials, dropping commodity malware, base64 encoded payloads, DNS tunneling for C2, customized LNK shortcuts, WinRAR and 7-Zip for compression and access to OWA. For a full list of tools, techniques and procedures, please refer to the reference section of this advisory.
HOW ISA CAN HELP
ISA’s digital forensics and incident response team with over 2 decades of experience, will analyze multiple data sources to determine the initial attack vector. We establish a timeline of activity and identify extent of compromise and risk to the business. This includes:
- Log analysis
- Host analysis
- Forensics analysis
- Memory analysis
- Network traffic analysis
- Malicious code analysis
Once indicators of terrorism related cyberattack are determined, our investigators collect the evidence and work with our clients to report the incident to law enforcement.
BE PREPARED
- Report suspicious activity to local law enforcement for Canada incidents, contact the RCMP. For US incidents, FBI, who are best to offer specific details on terroristic indicators.
- Be prepared for cyber disruptions, suspicious emails, and network delays.
- Be ready to preserve evidence
- Implement basic cyber hygiene practices such as effecting data backups and employing multi-factor authentication.
RISKS AND IMPACT AT A GLANCE
Risks | Business Impact | Major Impacts |
ICS SCADA | Operations delays Financial reporting delays | Loss of life Production delays Loss of product Loss of equipment |
Ransomware | Loss of productivity Loss of data | Financial, Regulatory and Litigative losses |
Website Defacement | Loss of reputation |
|
DDoS | Loss of productivity | Loss of revenue |
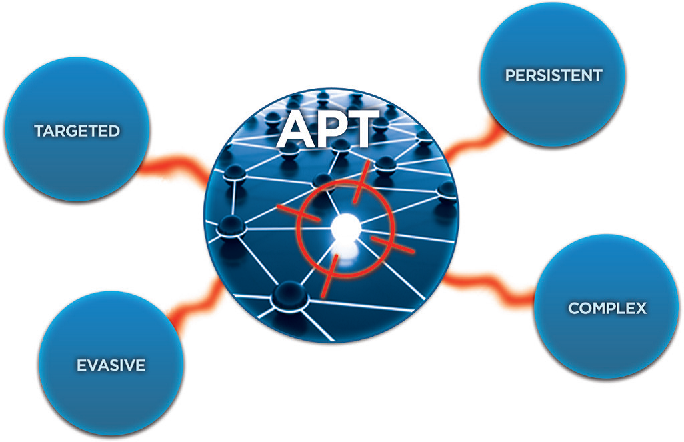
Target Industries by ADVANCED PERSISTENT THREATS
Group | Industry or Sector | Motivation |
APT 33 | Aviation, Defense, Energy, Petrochemical | Information Theft Espionage |
APT 34 | Chemical, Energy, Financial, Government and Telecommunications | Information Theft Espionage Sabotage |
APT 35 | Energy, Government and Technology | Information Theft Espionage |
APT 39 | Airlines, Airports, Engineering, Government, High-Tech, IT, Shipping and Logistics, Telecommunications and Transportation | Information Theft Espionage |
SAMPLE INDICATORS OF COMPROMISE
Nanocore
a5dc074b5cc998282abc9af1f4cecd4d
866e4ca19f5e205e80c4f858c87022b8
94a79ada20a57c2ff2bef429987746f8
a5e5de3c0e87c3c9de02946bccdc2e62
5c506713b2a4ca631e54fc8f62923aaa
njRAT
3ea4a80e7bea260548ecc21954cc6146
fa5494980fae77f0df84ea5ffdc99aa4
a68beb48f25fdc586decc2f8aeae7af4
cd55753092fd4dde924382d1c6a0e3bc
7c3be0252d129681437d6467f93d09fd
Netwire
860b420c406389ffd2e024850a8fe70d
25fb19518baa5600ce36a2456f6bb0e1
e77f2f736776f2367e1cef703cf5ef5b
c079412d8386f29ce40d0e8352cff96d
46a2b440ade1e8177ecb592317d0907c
QuasarRAT
d411675500ecd960f4f74af8ea41c57c
778c2454143135c80ea35618228a5f39
4af6b70747c2b7c2c70ea925ea6c465a
9a61905ca6c3030ef156e2afdfbfce6c
71f78d0836be785c8955179ba570c1b1